Which Are Used to Secure Data on Mobile Devices Quizlet
Follow these six steps to help keep your mobile device secure. Learn vocabulary terms and more with flashcards games and other study tools.

Quizlet Debuts Study Feature That Helps Students Study Efficiently Campus Technology
In short a PED is a portable electronic device for which there is no connection to the actual system.

. Start studying Mobile and Device Security. Virtual Desktop Infrastructure VDI allows a client device to access a VM. Remote lock allows the device to be locked from a remote location.
Your physical location or the locations of your. More and more mobile devices are used for accessing and storing business-critical data or other sensitive information. Quizlet is not popular among professors since it has been used for cheating.
SET UP A PASSCODE. Encrypt all sensitive data on laptops and on other mobile computing devices when possible At a minimum password protect Government-issued mobile computing devices. It revealed that corporate IT continues to struggle with how best to protect their organisations from data breaches viruses and other cyber-security issues brought on by employees using mobile devices.
Quizlet Plus for teachers. You just studied 10 terms. The survey revealed that 41 of respondents have lost 50000 100000 over the past three years due to a mobile device security breach or.
All mobile computing devices that store University of Florida Data must be fully encrypted regardless of ownership. Security Set Identifiers SSIDs can be turned off so that all devices will be unable to detect them. The most commonly reported cause of PII breaches is failure to encrypt e- mail messages containing PII.
Modems communicate data by using which method quizlet. The easiest way for someone to access the information on your phone is to simply snatch it. This means that personally owned laptops smartphones and tablets used for university business must be encrypted.
Mobile device management MDM is security software that enables IT departments to implement policies that secure monitor and manage end-user mobile devices. Hackers and data thieves can use Bluetooth connections to eavesdrop on your device and access your sensitive data. When investigating a mobile device after determining the device is safe to handle network connectivity should be disabled to avoid.
When using Bluetooth devices the following security precautions are critical for protecting the system. Software-based encryption - can encrypt individual files and folders entire disks removable media mobile devices and databases. Strong passwords coupled with biometric features such as fingerprint authenticators make unauthorized access nearly impossible.
Forensic tools typically access device data by taking advantage of a mobile OS vulnerability. Protecting the information on mobile devices is becoming a business imperative. The device and its software must be configured according to tested and established policies.
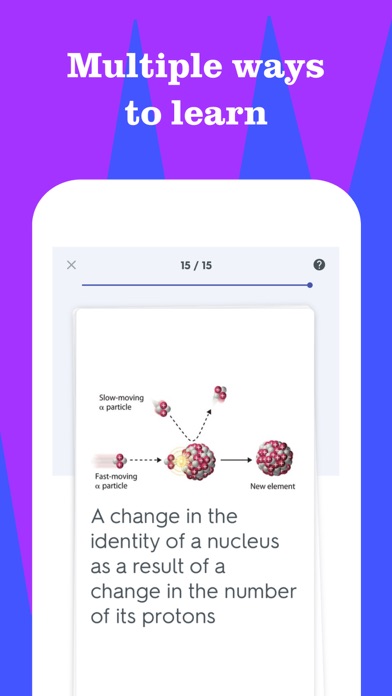
Personal data will not usually be erased from some mobile devices unless the number of failed passcode login attempts exceeds a threshold. Using Quizlet is easy and practical for different fields of study. Mobile devices are much more likely to be lost or stolen so you should consider encrypting data on your mobile devices.
Mobile Device Management MDM Defined. Cannot be done offline. These devices are typically consumer electronic devices that conduct communication as well as processing data.
Learn vocabulary terms and more with flashcards games and other study tools. A modem converts data to a signal so it can be easily sent and received over a phone line cable or satellite connection. Follow your organizations policies on the use of mobile computing devices and encryption Use only mobile devices approved by your organization Encrypt all CUI nci udil ng P II on mobie devl ci es and when e- mailed.
Quizlet as an additional study tool is effective for rote memorization. Mobile Device Security Due Mar 22 at 1159pm Points 35 Questions 26 Available after Mar 14 at 8am Time Limit None Allowed Attempts Unlimited Attempt History Attempt Time Score LATEST Attempt 1 14 minutes 35 out of 35 Score. It is easy to learn incorrect information through the available study decks unless there is a verified badge.
Photos and music on remote servers for download to iOS Macintosh or Windows devices to share and send data to other users. Forensic tools typically access device data by taking advantage of a mobile OS vulnerability. Finding a solution to this data security issue is even more important today because mobile devices routinely store more of employees data in the cloud.
While we are seeing a growing number of mobile users who are adopting security solutions less than 1 of corporations actually deploy a mobile malware solution. - manufacturers app store Google Pay iTunes etc - Enterprise management tools Exchange Server - security tools Lookout AVG device must be connected to cell networkWiFi. Help to secure a mobile device and the transactions made on websites through that device.
The router will only drop non delay-sensitive data that is close to the end of the queue. Consider disabling Bluetooth connectivity on your device unless you need it. This is the true backdoor to our.
The passcode lock feature on mobile devices helps prevent theft of private information and places the device into a power saving state. Which US carrier primarily used the IDen standard. Used when device is stolenlost.
Quiz 10 Chapter 10. What Are Portable Electronic Devices. For example smartphones and tablets store University of Florida Data when they are configured to access UF email.
In this scenario the mobile device is the client device. Accidently calling a friend. In order to feel more secure about mobile devices and people storing information remotely you need to trust that the cloud can protect your data once it leaves the devices.
Accepts a frame from a medium 2. Start studying FedVTE Mobile and Device Security. Consider disabling Global Positioning System GPS and other location services unless you need them.
Corporate data is stored and processed on the VM so there is less chance of it being compromised even though the client device itself is not fully managed. Free to all Apple device owners and provides 5GB of remote cloud storage space for backing up Apple iPhone iPad. Primary methods of protecting the confidentiality of data including data at rest and data in transit are encryption and strong access controls.
Question 11 Mobile devices with global positioning system GPS abilities typically make use of. Sends command to remotely clear all data on device. When youre in.
Use two-factor authentication if possible Secure your personal mobile devices to the same level as Government-issued systems. This not only includes smartphones but can extend to tablets laptops and even IoT Internet of Things devices. Here are some practical steps that will help you minimize the exposure of your mobile device to digital threats.
Laptops tablets ebook readers smartphones MP3 players drones electronic toys and MP3.
Quizlet Debuts Study Feature That Helps Students Study Efficiently Campus Technology

Unit 3 Storage Devices And Media Flashcards Practice Test Quizlet

Freepsdhtml Best 80 Free Ipad Mockups Psd Free Download Mockup Free Psd Ipad Mockup Ipad Mockup Psd

Tiktok Is Partnering Up With Quizlet A Popular Online Education Platform That Helps Users Online Education Online Study Teaching

Quizlet Is Now 100 Secured With Https Quizlet

Chapter 1 Mobile Devices Flashcards Practice Test Quizlet

Global Learning Platform Quizlet Launches Free Gcse Resource Centre For Uk Teachers Students Fe News

Quizlet Elementary School Learning Learning Tools Literacy Resource

Quizlet App Cover App Covers App Icon Homescreen

Domain 1 0 Mobile Devices Flashcards Quizlet

Computer Science Principles Vocabulary Flashcards Quizlet Computer Science Science Vocabulary
Quizlet Learn With Flashcards For Android Download Free Latest Version Mod 2022

Unit 2 Input And Output Devices Flashcards Quizlet
Quizlet Learn With Flashcards For Android Download Free Latest Version Mod 2022

Network Security Flashcards Quizlet

Ch 9 Operating Systems Flashcards Quizlet
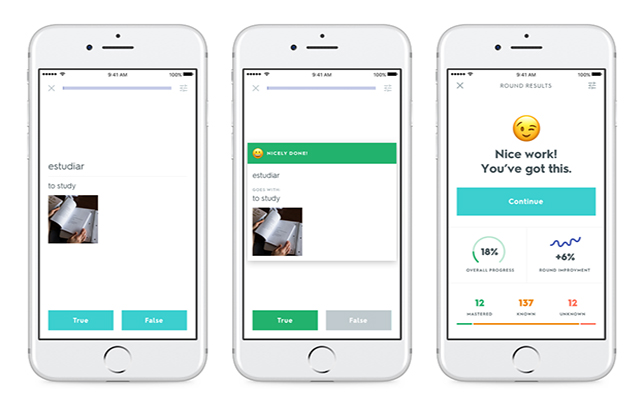
Quizlet Debuts Study Feature That Helps Students Study Efficiently Campus Technology


Comments
Post a Comment